Did Facebook partner with Kaspersky Lab to push hacked Russian malware software on its users during the election?
This week it was revealed that the Russians took advantage of Kaspersky Lab anti-malware software on an NSA contractor’s home computer in order to hack into sensitive data (New York Times). This has been just the latest blow to the reputation of Kaspersky Lab, which is headquartered in Moscow and is now suspected of having played a key role in the hacking of the 2016 election. In an exchange with Kaspersky Labs, a rep has informed Palmer Report that it is partnered with Facebook to actively push its software on Facebook users.
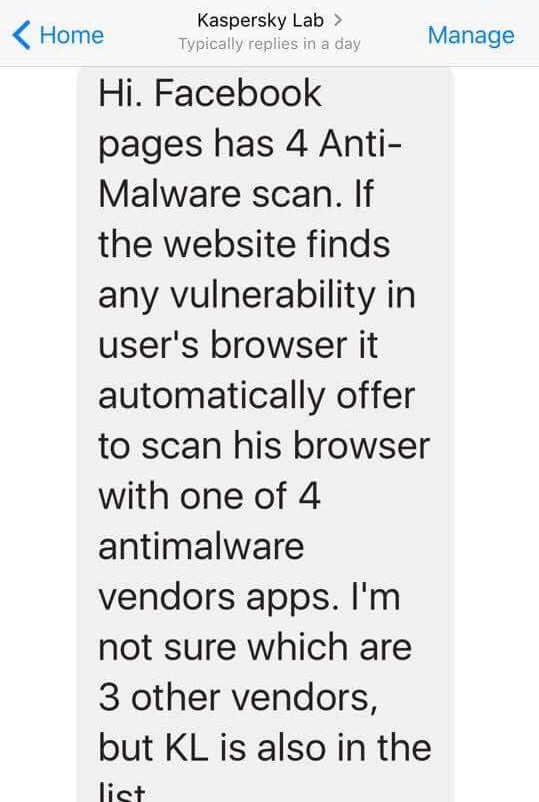
Palmer Report contacted Kaspersky Lab by sending a message to its official verified Facebook page (link), inquiring as to the company’s affiliation with Facebook. Here is the verbatim response we received, which was sent back to us by an unnamed company rep and is in slightly broken English: “Hi. Facebook pages has 4 Anti-Malware scan. If the website finds any vulnerability in user’s browser it automatically offer to scan his browser with one of 4 antimalware vendors apps. I’m not sure which are 3 other vendors, but KL is also in the list. If Facebook offers to scan it seems Facebook’s engine found a vulnerability in your browser.”
Our communication with Kaspersky’s official Facebook page:

Kaspersky’s response to our query:
This serves to reignite an earlier debate about whether Facebook was actively pushing the compromised Kaspersky software on its users during the 2016 election. Seven days after Donald Trump officially announced he was entering the election, a note appeared on Facebook which purported to be coming from “Facebook Security” (link). The note announced a partnership between Facebook and Kaspersky Lab, in which Facebook would auto-detect malware on a user’s computer and then require the user to download Kaspersky anti-malware software. That same day, Kaspersky posted a press release on its own official website (link), announcing the supposed partnership.
At least two respected news outlets, AdWeek (link) and Beta News (link), interpreted the above note as having been an official Facebook communication. Facebook users have long debated as to whether the note was truly from Facebook itself, or was part of a scam which was merely set up on a Facebook page. Numerous users have reported over the past two years that their Facebook accounts have indeed been taken over by a notification forcing them to download the Kaspersky software. From these reports, it’s never been entirely clear if Facebook itself was pushing the Kaspersky software, or if this was some sort of phishing scam being run on Facebook without Facebook’s knowledge.
We’ve attempted to track down the Facebook Threat Infrastructure software engineer, Trevor Pottinger, who is credited with having written the supposedly official Facebook announcement about the Kaspersky software. He has a LinkedIn page claiming that he is indeed a Facebook engineer (link). However, aside from news reports that are sourced directly back to the note in question, we can find no evidence to confirm or refute that he does indeed represent Facebook and that the note was legitimate.
We’re continuing to attempt to determine whether or not Facebook itself is officially involved in the effort to push Kaspersky Lab software on Facebook users. But Kaspersky itself has been purporting to be partnered with Facebook to deliver its software to users since shortly after Donald Trump entered the race, up through the present day. Either Facebook is participating in a highly suspicious partnership with a compromised Russian software company, or Facebook and its users are unwittingly being victimized by that company. Either way, in light of current events, this demands further investigation.
